Cyberattacks pose an increasingly serious threat to businesses. According to Bitkom, the annual damage to the German economy amounts to more than 200 billion euros. Many companies assume the most important protective measure is to buy and operate a set of expensive IT security products. However, this is a misconception that can have far-reaching consequences, because in practice, IT security is not a product you can buy; it is only achieved through a continuous, holistic process.
The IT security world is full of buzzword-heavy marketing promises that often turn out to be little more than hot air. As a result, important fundamentals that are essential for secure IT operations unfortunately fade into the background. The reason is obvious: software solutions that promise relief through simple installation are much easier to market than a continuous process that requires the company itself to take action.
Products such as antivirus solutions can provide an additional hurdle for attackers within a defense-in-depth model, but they must never be the main protective measure. For example, during our ransomware simulations, we repeatedly see that our custom-developed ransomware is not detected by antivirus software. This also reflects the reality of ransomware attacks, since almost all victims use antivirus solutions. That does not seem to bother criminals: nationwide, at least one new ransomware attack is recorded by police every day, with an estimated dark figure of up to 90 percent.
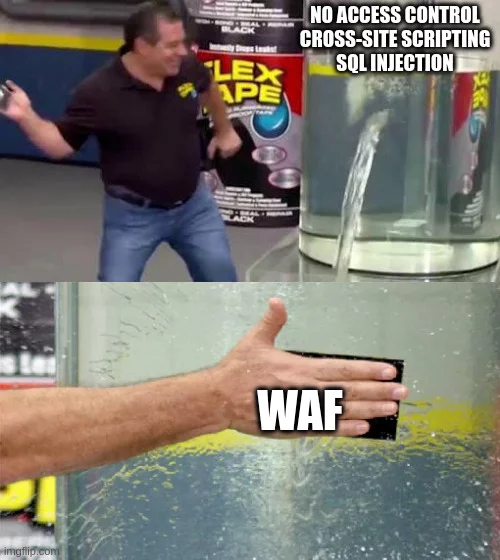
When operating web applications, many companies use so-called web application firewalls (WAFs) that can detect and block malicious requests, and they assume that vulnerabilities in the underlying web application no longer matter. While WAFs do make it harder to exploit existing vulnerabilities, they can still be bypassed, which we regularly achieve in our penetration tests. It is therefore important to integrate IT security into the software development process so vulnerabilities do not arise in the first place.
In an IT system where key basic principles are not followed, such products are like a band-aid on a deep flesh wound. One of these principles is effective patch management, because technically speaking, outdated software is the largest entry point for attackers who exploit known vulnerabilities to infiltrate systems. Rapid installation of security updates is therefore essential to make attacks as difficult as possible.
In addition, during our penetration tests we often find that simple but important hardening measures for the internal network are not implemented. Easily disabled default settings in the Active Directory environment enable an attacker who has already penetrated the internal network to spread unchecked and take over the entire IT system. Here, too, no product can solve the problem; the existing system must be securely configured by system administration.
However, implementing only technical measures is not enough, because for attackers, social engineering attacks such as phishing emails are usually the first step to gain access to internal networks. The reason is that in most cases, the human factor is easier to bypass than technical systems. During our phishing campaigns, we often succeed in obtaining the passwords of more than 20 percent of all employees, an alarming figure considering that in the worst case, a single success is enough to cause major damage. Raising employee awareness of such attacks is therefore essential.
To effectively protect itself against cyberattacks, a company must take responsibility for its IT security and integrate it into its own processes. Software products and services can provide support, but they are not a cure-all. To determine the current security level, it is advisable to conduct regular security assessments such as penetration tests or phishing campaigns. We at CRISEC are happy to support you.