Phishing emails are currently the most common entry point for cyberattacks. Many companies believe they are fully protected by using multi-factor authentication (MFA), but there are now new attack methods that can bypass MFA.
Man-in-the-Middle (MitM) Phishing
The newest tool in attackers’ toolbox is so-called man-in-the-middle (MitM) phishing. Here, the attacker places themselves in the middle between the user and the real login server by using a reverse proxy, and can obtain a valid user session despite MFA.
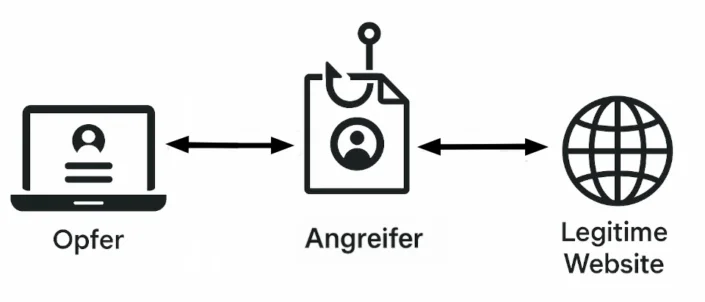
The attacker first presents the user with their phishing page as usual. When the user enters their credentials, the most important part of the attack has only just begun. In the background, the attacker forwards the credentials to the real login server (e.g., login.microsoftonline.com) and receives an MFA challenge in return.
The attacker now displays this MFA challenge to the user on the phishing page. The user confirms it, for example via the Microsoft Authenticator app, after which the real login server signs them in.
But remember that the real login server is only communicating with the attacker. So the attacker receives the session cookie that authenticates them to the web application. This means the attacker was able to obtain a valid user session despite MFA being enabled.
Since most companies now use MFA for external access to company resources, this method is increasingly being used by cybercriminals. Relevant tools are even partly offered on the dark web as so-called phishing-as-a-service offerings, which means even less technically skilled attackers can exploit this technology.
How can I protect myself?
MitM phishing is therefore an attack companies must expect, and we have seen that MFA alone is not enough protection. So what additional measures are required?
A first step is sensible conditional access policies in the Microsoft 365 environment. For example, if a login attempt comes from Russia even though all employees are in Germany, you can assume the login is illegitimate and lock the account. This so-called geofencing can already block many attacks, since they often come from abroad.
Another example of a conditional access policy is when a user is already logged in from an IP address in Frankfurt, but another login attempt comes from an IP address in Hamburg. Since this so-called “impossible travel” is not possible, this can also be treated as an attack.
A technical solution that completely prevents phishing of credentials is the use of passkeys. With passkey authentication, users sign in with a cryptographic key instead of a password. Because passkeys can only be used on the correct domain, a user cannot authenticate with them on a phishing site.
In addition to standard training measures, we also recommend running regular phishing campaigns to give employees practical exposure to the issue in their daily work and improve awareness.
In addition to classic phishing campaigns, we also offer testing of existing conditional access policies and evaluation of how well you are protected against MitM phishing.